Bolstering Healthcare Information Security, Part Two

In a recent article we examined the healthcare industry’s unique and pronounced vulnerability to cyberattack. In this article, we examine best practices for healthcare providers to protect themselves from security breaches by looking at steps we have taken at FRG and what the literature suggests.
Strategically, it is always important to perform an information security risk assessment with a professional consultant. When it came time for FRG to pursue HiTrust CSF Certification, we hired a team of experts to help us develop a robust and complete answer to hardening our already thorough approach to information security against acts of malicious cybercriminals. We recommend finding consultants you trust to guide you, integrating their advice into your operating strategy and then adding staff to ingrain their guidance into your core processes.
Our consultants helped us think through decisions about infrastructure configuration, develop approaches to enable secure collaboration, implement training programs to ensure staff awareness of risks and design robust processes for information protection, service continuity and business resilience. This wholistic approach made the exercise more about corporate fortitude than the narrow focus of cybersecurity, and we’re better for it.
In the literature, readers will discover that this is a common approach. Protecting an organization hinges on the way employees perceive the risk, behave in the context of the environment and use the tools they are given to perform their job functions. When framed in this way, the project to protect the enterprise can be distilled into a three-pronged approach, as described below.
A Three-Tiered Approach to Protecting Healthcare Data
There are three broad areas where healthcare providers can strengthen their defenses against online attacks of all types:
- Employee Training and Awareness
- Behavior Modification
- Technology Infrastructure
Each of these prongs overlap, helping to reinforce the system and prevent cybercriminals from exploiting gaps.
Employee Training and Awareness
Raising awareness of the risks to information security is the first step in ensuring that structural safeguards deployed later will not be circumvented as a result of cavalier attitudes.
Citing a 2016 survey by Experian Data Breach Resolution and Ponemon Institute, an article in Healthcare IT reports that more than half of all business-related data breaches were caused by “employee error.” In the same survey, 66 percent of respondents said that employees were the “biggest challenge to developing and implementing robust data security postures.”
Experian Data Breach Resolution Vice President Michael Bruemmer said the study “emphasizes that the risk of a data breach caused by a simple employee mistake” drives many data security breaches. “Unfortunately,” said Bruemmer, “companies continue to experience the consequences of employees either falling victim to cyberattacks or exposing information inadvertently.”
Employee awareness does not eliminate the risk of inadvertent error but it goes a long way in reducing it. We recommend enrolling in one of the many web-based training tools that help to explain how historical breaches occurred and teach lessons on how to avoid them in your own organization. Lessons that are short and fun are much easier to complete, and staff are more likely to retain the lessons if they include a quiz component.
At a minimum, employees should be made aware of the trends in the industry, the known approaches by cybercriminals and the risks to the company and the best practices (“do’s and don’ts”) of behaving with information security top of mind. Employees should also be trained on the tools that the company has deployed to help them act on their awareness.
Behavior Modification
Once staff have been trained, behavior modification is possible. Expectations are set through policy, communicated through training, and compliance is required. Compliant behavior is classically encouraged through positive and negative motivators, and a combination of rewards and penalties can be integrated into conversations about information security.
Indeed, the most negative motivator is that which the whole program is intended to guard against, and the penalties to the organization and the employee can be severe depending on the circumstances. However, designing an award system that also integrates positive incentives for compliance can increase involvement in training and encourage vigilance in safeguarding efforts, thereby serving to build a corporate culture that guards against the risk.
Prizes for perfect scores on training completed on time, bonus payments for incident-free periods, and parties to celebrate assessment scores can reinforce positive behaviors and ensure compliance with corporate policies designed to safeguard information and the enterprise.
Taking a Defensive Posture
The positive and negative motivators should put an organization in a position of confidence and strength, but with awareness of risk, the essence of a defensive posture.
The risks of not taking this approach are only growing. Attacks have become more sophisticated and ubiquitous. Due to the “sophistication and variety” of attacks, it may be difficult to have a culture of confidence in the company’s ability to counter a determined attack. This is a dangerous mindset. It can lead to a fatalistic perspective of resigned complacency, leaning too much on the odds that such a determined attack will not ever happen. Unfortunately, failing to prepare is not acceptable to insurers or regulators, so prepare and be confident!
On average healthcare firms take 236 days to identify security breaches and 83 days to contain them – two months longer on average than any other industry. A report cited in Healthcare IT News notes that most healthcare organizations have formal incident response protocols in place. Only 15 percent have fully implemented security automation tools. Half have no security automation at all. This is not taking a defensive posture and partially explains the sluggish response times.
In the same article, Christopher Scott, chief technology officer and global remediation lead at IBM X-Force says that appropriate incident response planning must have “priority among C-Suite level and upper management executives.”
When employed at all, incident response planning is often “siloed or ad-hoc,” says Scott. An effective defensive posture requires a comprehensive plan applied to an “entire organization.”
Defensive posturing does not include leaving your right flank unguarded. Engage the training, and behavior coaching approach throughout the organization to reduce the chances of penetration and limit the scope of damage in the event something does happen.
The Problem of Phishing
Defensive posturing is important because things do happen, like phishing attacks. The examples of phishing abound. An email ostensibly from a trusted colleague urges a specific action – clicking a link, downloading a file – from the recipient. If the link is clicked or the file downloaded, the keys to the kingdom can be lost, exposing patient records or other confidential data and opening your organization up to ransomware attacks.
Phishing attacks are not new, but they still work. The baited hook of a phishing attack that only takes one distracted employee duped by a scam email to inadvertently open the door. Two basic approaches protect against phishing attacks:
- Training programs that periodically remind us of the risk of phishing and the ways attacks are evolving should serve to proactively reminded employees of the risk of phishing and other more sophisticated attack methods.
- Emails from outside of the organization should be flagged so that the reader knows to proceed with caution.
Sample Message Header Flags:
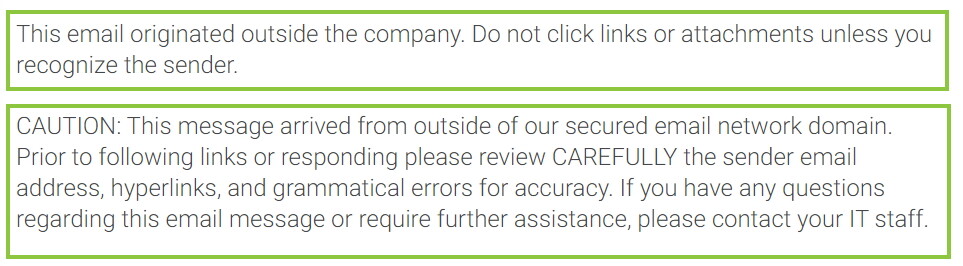
Employees receiving messages from outside the organization should heed these warnings! Hovering over doubtful hyperlinks can help quickly determine if the link is a trap, and if it is not recognizable, take pause.
Technology Infrastructure
Employee training and behavioral modification impact infrastructure and technology in fundamental and often surprising ways. A feeling of being “outmatched” by cybercriminals as we described earlier can manifest itself in ways that ensure an organization is, in fact, thoroughly unprepared for the consequences of a data breach.
Empowering trained employees with secure networks, up-to-date operating systems and multi-factor authentication technologies can turn the tables. Resting on legacy system, however, has strategic tradeoffs of switching cost vs costs of a negative outcome. Of course this analysis is done in a probabilistic style, but the likelihood of an event is rising and the cost of the same is astronomical, so the scales are quickly tipping – if they haven’t already – to taking the action necessary to achieve a defensive posture.
Intractable Legacy Systems
A July 2019 article in IT Healthcare News shows that 54 percent of all U.S. healthcare providers still use legacy Windows 7 operating systems. Not surprisingly, this leaves an enormous vulnerability to “malware and other cyberattacks like WannaCry,” the article says. Cybercriminals know this and take full advantage of it.
The global WannaCry ransomware attack in 2017 crippled 300,000 machines in 150 countries. Even though Microsoft issued a patch after the initial attack, many organizations failed to install it in their systems. Three years later it remains a serious threat.
The importance of maintaining up-to-date operating systems and immediately installing patches can’t be emphasized enough. Not doing so can make any other security effort moot.
Hardened Environments
There are many approaches to building a secure technology infrastructure that an organization can pursue with designing or refining its approach. The NIST CyberSecurity Framework and the HiTrust CSF Framework both provide guidelines to help organizations design and implement technology infrastructure components and business processes to protect information security and patient privacy.
Leveraging some of the resources on these sites to conduct an independent risk assessment is a first step. Then connecting with a trusted advisor to coordinate evaluation of the myriad of controls – sometimes hundreds – to achieve and maintain compliance is the next. Along the way, don’t forget a BYOD policy.

While healthcare organizations will continue to be targeted, this three-tiered approach can help companies meet the challenges of data security, risk management, and protecting sensitive patient information. While embracing the charge of taking a defensive posture, recall that President Ronald Regan was famous in the 1980’s for quoting Roman Emperor Hadrian’s adage of achieving “Peace Through Strength.” In the modern digital age, building a wall is often not enough to keep out the barbarians. A secure network is absolutely necessary, but Romans* on the inside also need to know not to open the gates!

Editor’s Note: According to Virgil’s Aeneid, Rome was founded by the defeated Trojans who fled Troy after the Greeks gave them a horse statue in which warriors were hidden and which the Trojans (foolishly) brought inside their impenetrable fortification. The rest is history.
Great post!